Standard backups are no longer enough
By MYBRANDBOOK

Amit Deshmukh
Head - India Channels and Distribution Business, Cohesity
New ransomware variants destroy backup data before they encrypt production data. Therefore, companies need intelligent security solutions in combination with secured data that cannot be changed.
In some ways, the competition between cybercriminals and security experts resembles the famous race between hare and tortoise. At first, hackers primarily encrypted production data. Companies fought back with solutions that allowed data to be restored quickly via backups.
Then the attackers shifted to destroying or encrypting backups. IT countered with immutable backups. Now the criminals are pulling data and threatening to publish it on the dark web. As a result, companies are once again faced with the question of how to adequately secure their data.
AI instead of traditional tools
Many conventional or legacy tools only detect attacks using known virus signatures, IP addresses or attack patterns. However, they often cannot detect and defend against new types of attacks from unknown sources.
To defend against current attacks, companies should therefore also deploy next-gen data management solutions with built-in artificial intelligence and machine learning (AI/ML) capabilities. These technologies can be used to trigger alerts that can notify the IT data admin when the backup data changes or ingest rates fall outside the norm based on historical trends - all of which could indicate an attack has taken place.These capabilities can also indicate, for example,when a user accesses large amounts of sensitive data at unusual times. Integration with security orchestration, automation, and response (SOAR) platforms can then be used to trigger defensive measures or further authentication via an additional factor.
Companies should complement this with an integrated data security and data governance solution. They can then use AI/ML systems to classify their data to identify sensitive information - including personal data. Only when it is known what sensitive data is stored where can it be determined who has access to it to protect it from attack. Data classification with predefined guidelines, such as data protection regulations and legislation, helps make compliance easier.
Immutable backups
Despite all precautions, a data theft or ransomware attack can be successful. In this case, companies need the ability to restore data quickly. But the backups must not have been altered beforehand, for example through unwanted encryption or deletion by an attacker. Therefore, it’s critical that customers embrace next-gen solutions that offer immutable back up snapshots. Immutability helps ensure that no unauthorized user or application can modify the ‘gold’ copy of the backup. Any attempts to modify the ‘gold’ copy will automatically create a zero-cost clone.
If this feature is embedded from the start, the original copy of the data is safer from unwanted manipulation. In addition, it is recommended to activate DataLock in the backup policy. The snapshot is then provided with a time-limited lock that even the security officer cannot delete.
For even greater security, look for solutions that provide data on the frequency of file accessed, and the number of files that are modified, added to, or removed by a particular user or application.
There is also the option to store an isolated copy in an externally managed data vault. This makes data even more resistant to ransomware attacks. In addition to immutability, this gives companies another way to protect themselves from attackers who want to encrypt data.
Last but not least, in the event that you are attacked, recovering quickly is the name of the game. Therefore, look for next-gen data management solutions that offer instant mass restore capabilities so that you can minimize downtime while keeping the brand intact and customers happy.
Relying on traditional backups as insurance is no longer enough. Modern systems offer AI/ML solutions to detect and defend against even novel attacks. Should they still succeed, immutable backups can help enable fast and reliable data recovery.


Legal Battle Over IT Act Intensifies Amid Musk’s India Plans
The outcome of the legal dispute between X Corp and the Indian government c...

Wipro inks 10-year deal with Phoenix Group's ReAssure UK worth
The agreement, executed through Wipro and its 100% subsidiary,...

Centre announces that DPDP Rules nearing Finalisation by April
The government seeks to refine the rules for robust data protection, ensuri...

Home Ministry cracks down on PoS agents in digital arrest scam
Digital arrest scams are a growing cybercrime where victims are coerced or ...


ICONS OF INDIA : SANDIP PATEL
Sandip Patel is the Managing Director for IBM India & South Asia regio...

Icons Of India : AALOK KUMAR
Aalok Kumar is celebrated as a global leader and recipient of the Peop...

ICONS OF INDIA : VIJAY SHEKHAR SHARMA
Vijay Shekhar Sharma is an Indian technology entrepreneur and multimil...


ITI - ITI Limited
ITI Limited is a leading provider of telecommunications equipment, sol...

IREDA - Indian Renewable Energy Development Agency Limited
IREDA is a specialized financial institution in India that facilitates...
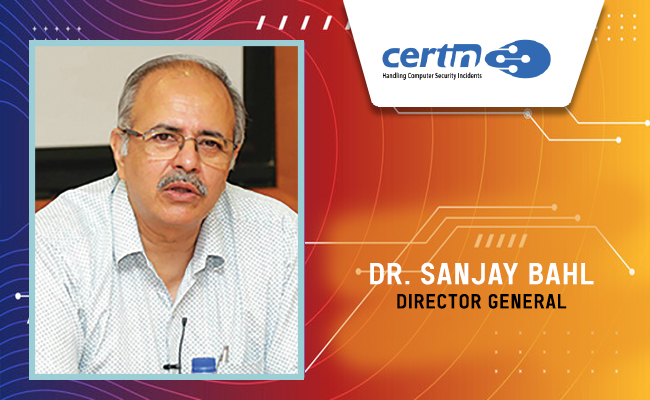
CERT-IN - Indian Computer Emergency Response Team
CERT-In is a national nodal agency for responding to computer security...

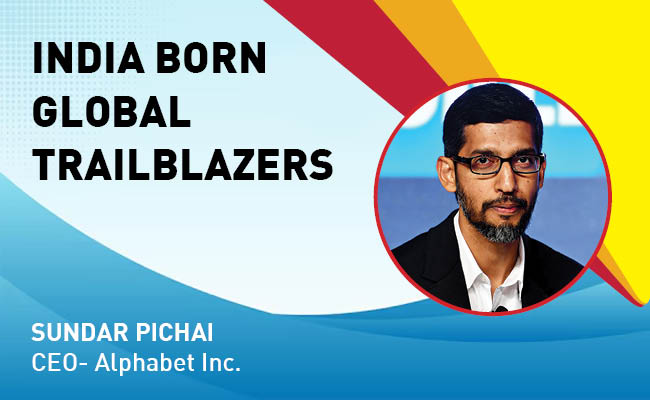
Indian Tech Talent Excelling The Tech World - Sundar Pichai, CEO- Alphabet Inc.
Sundar Pichai, the CEO of Google and its parent company Alphabet Inc.,...

Indian Tech Talent Excelling The Tech World - NEAL MOHAN, CEO - Youtube
Neal Mohan, the CEO of YouTube, has a bold vision for the platform’s...
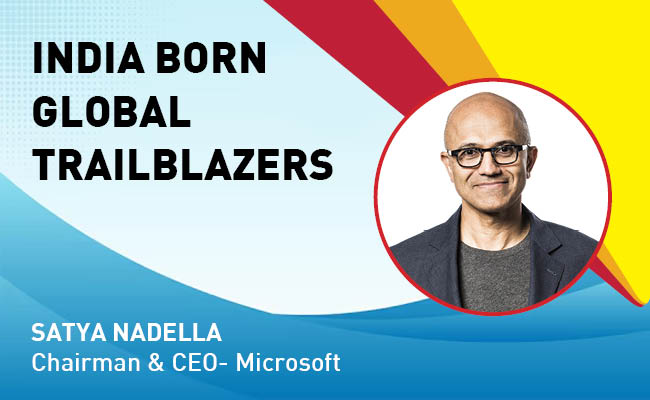
Indian Tech Talent Excelling The Tech World - Satya Nadella, Chairman & CEO- Microsoft
Satya Nadella, the Chairman and CEO of Microsoft, recently emphasized ...
 of images belongs to the respective copyright holders
of images belongs to the respective copyright holders