Is your PC being used for cryptocurrency mining?
By MYBRANDBOOK
It is a fact that, new technologies in the Information age will bring newer challenges and risk at the same time. There is a potential risk in adopting newly emerged technologies. For instance, Artificial Intelligence (AI) holds tremendous potential to automate daily risk activities, and rationalize costs. Blockchain technology will enable companies to manage and share GRC information faster than ever, whether it is around vendor risk assessments or continuous auditing. Robotics is all about automation, increasing efficiency and providing intelligence that cannot be seen with the human eye. The cloud, in turn, is enabling the seamless flow of data and Information assets include personal information. Security is one of the main enablers of data protection. It is an absolute fact that about millions of PCs are being used for stealth of cryptocurrency mining. It is advisable to block cryptocurrency mining in your browser.
The threat landscape is constantly evolving and the biggest cost associated with mining is the hardware to mine and the electricity to power the mining hardware. By leveraging malicious miners attackers can take both of those costs out of the equation altogether. Since they are able to take advantage of computing resources present in infected systems, there is no cost for power or hardware and attackers receive all the benefits of the mined coin. Your PC may be used to find cryptocurrency with or without your consent.
The biggest challenge is however on the IoT devices (Internet of Things (IoT) that makes it easy for you to control devices around your home) and bots (Bots allow users to consume a service without the need to download and ‘learn’ a new app0. Bots also operate using natural language, so the barrier for a new user to interact with a bot is really low. Bots provide the ideal interface for an IoT-enabled smart devices, and with their lack of monitoring and lack of day to day user engagement, they are fast becoming an attractive target for these attackers, as they offer processing power without direct victim oversight. While the computing resources within most IoT devices are generally limited, the number of exposed devices that are vulnerable to publicly available exploits is high which may make them attractive to cyber criminals moving forward.
search websites, domains hosting pirated content, and pornographic websites are the most likely to use cryptocurrency miners. Cybercriminals have taken advantage of cryptocurrency mining in order to make a profit. However, they generally use malware or applets (potentially unwanted applications) they install on the victim’s machine in order to turn a dishonest penny. The main target is the Websites with video-based content that keep users in place for some time are most likely to generate income from this method, with this they can trigger the System Objects including system files of root operating System. If you have activated your SSL Mechanism along with malware protection option, you may be safe but have to verify your system log information for the same.
Bitcoin mining or cryptocurrency mining software are acquired through the computational power and is not malware. If enough PC owners donate power, then mining can be a way to rake in revenue. The software itself is used to leverage computing power -- such as a visitor to a webpage's CPU -- to mine for cryptocurrency such as Monero. As per a survey, in a matter of weeks, 2.2 percent of the top 100,000 websites on the Alexa list are now mining through user PCs. In total, 220 sites launch mining when a user opens their main page, with an aggregated audience of 500 million people. CoinHive and JSEcoin are currently the most popular scripts being employed to hunt down cryptocurrency.
When customers buy a bitcoin mining contract then they will begin earning Bitcoins instantly. However, if domain operators do not respect their end users and do not seek permission, they are risking a hit to their reputation which they may not recover from. Until this issue is resolved, take note -- adblockers will generally block these scripts.


Legal Battle Over IT Act Intensifies Amid Musk’s India Plans
The outcome of the legal dispute between X Corp and the Indian government c...

Wipro inks 10-year deal with Phoenix Group's ReAssure UK worth
The agreement, executed through Wipro and its 100% subsidiary,...

Centre announces that DPDP Rules nearing Finalisation by April
The government seeks to refine the rules for robust data protection, ensuri...

Home Ministry cracks down on PoS agents in digital arrest scam
Digital arrest scams are a growing cybercrime where victims are coerced or ...


ICONS OF INDIA : SANJAY GUPTA
Sanjay Gupta is the Country Head and Vice President of Google India an...

Icons Of India : Debjani Ghosh
Debjani Ghosh is the President of the National Association of Software...

ICONS OF INDIA : RISHAD PREMJI
Rishad Premji is Executive Chairman of Wipro Limited, a $11.3 billion ...


NSE - National Stock Exchange
NSE is the leading stock exchange in India....

CSC - Common Service Centres
CSC initiative in India is a strategic cornerstone of the Digital Indi...

GSTN - Goods and Services Tax Network
GSTN provides shared IT infrastructure and service to both central and...

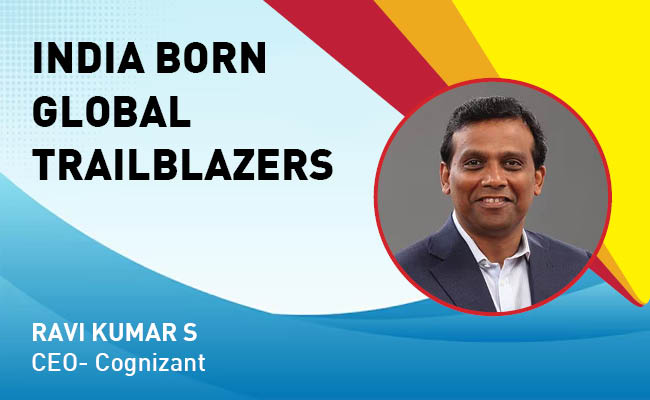
Indian Tech Talent Excelling The Tech World - RAVI KUMAR S, CEO- Cognizant
Ravi Kumar S, appointed as CEO of Cognizant in January 2023, sets the ...
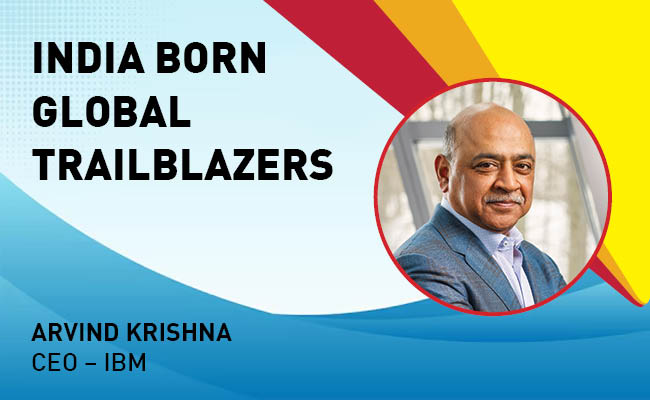
Indian Tech Talent Excelling The Tech World - ARVIND KRISHNA, CEO – IBM
Arvind Krishna, an Indian-American business executive, serves as the C...
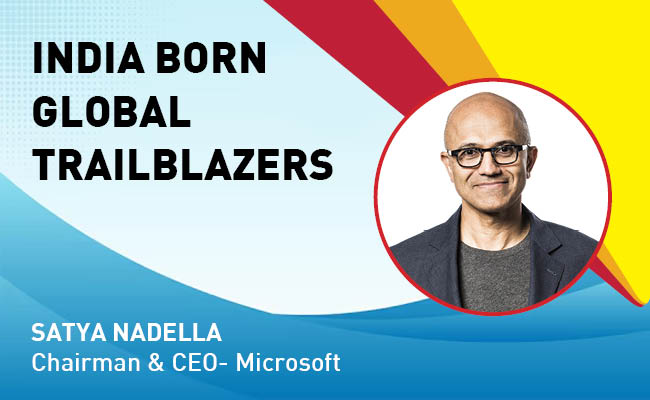
Indian Tech Talent Excelling The Tech World - Satya Nadella, Chairman & CEO- Microsoft
Satya Nadella, the Chairman and CEO of Microsoft, recently emphasized ...
 of images belongs to the respective copyright holders
of images belongs to the respective copyright holders