New Attack Opportunities for Cybercriminals
By MYBRANDBOOK
Fortinet's recent announcement on the findings of its latest quarterly Global Threat Landscape Report. The reprt reveals that cybercriminals are constantly evolving the sophistication of their attacks—from continuing to exploit the vast insecurity of IoT devices, to morphing open source malware tools into new threats. For a detailed view of the Threat Landscape Indices for exploits, botnets, and malware, as well as some important takeaways for CISOs read the blog.
Key Highlights of the report :
· Exploit Index All-time High: According to the Fortinet Threat Landscape Index, cybercriminals remained hard at work even during a holiday season. After a dramatic start, the Exploit Index settled in the latter half of the quarter. While cyber adversary activity overall subsided slightly, the number of exploits per firm grew 10%, while unique exploits detected increased 5%. At the same time, botnets become more complex and harder to detect. Time for infection of botnets increased by 15%, growing to an average of nearly 12 infection days per firm. As cybercriminals employ automation and machine learning to propagate attacks, security organizations need to do the same to combat these advanced methods.
· Monitor the Monitoring Devices: The convergence of physical things and cybersecurity is creating an expanded attack surface, one that cybercriminals are increasingly targeting. Half of the top 12 global exploits targeted IoT devices, and four of the top 12 were related to IP-enabled cameras. Access to these devices could enable cybercriminals to snoop on private interactions, enact malicious onsite activities, or gain an entry point into cyber systems to launch DDoS or ransomware attacks. It is important to be aware of hidden attacks even in devices we use to monitor or provide security.
· Tools Open to Anyone: Open source malware tools are very beneficial to the cybersecurity community, enabling teams to test defenses, researchers to analyze exploits, and instructors to use real-life examples. These openware tools are generally available from sharing sites such as GitHub, and as these are available to anyone, adversaries can also access them for nefarious activities. They are evolving and weaponizing these malware tools into new threats, withransomware comprising a significant number of them. An example where openware source code has been weaponized is the Mirai IoT botnet. An explosion of variants and activity continues to be catalogued since its release in 2016. For cybercriminals innovation continues to be the land of opportunity.


Legal Battle Over IT Act Intensifies Amid Musk’s India Plans
The outcome of the legal dispute between X Corp and the Indian government c...

Wipro inks 10-year deal with Phoenix Group's ReAssure UK worth
The agreement, executed through Wipro and its 100% subsidiary,...

Centre announces that DPDP Rules nearing Finalisation by April
The government seeks to refine the rules for robust data protection, ensuri...

Home Ministry cracks down on PoS agents in digital arrest scam
Digital arrest scams are a growing cybercrime where victims are coerced or ...


Icons Of India : RAJENDRA SINGH PAWAR
Rajendra Singh Pawar is the Executive Chairman and Co-Founder of NIIT ...

ICONS OF INDIA : SUNIL BHARTI MITTAL
Sunil Bharti Mittal is the Founder and Chairman of Bharti Enterprises,...

Icons Of India : Deepak Sharma
Deepak Sharma spearheads Schneider Electric India. He brings with him ...


UIDAI - Unique Identification Authority of India
UIDAI and the Aadhaar system represent a significant milestone in Indi...

BEL - Bharat Electronics Limited
BEL is an Indian Government-owned aerospace and defence electronics co...

BSE - Bombay Stock Exchange
The Bombay Stock Exchange (BSE) is one of India’s largest and oldest...

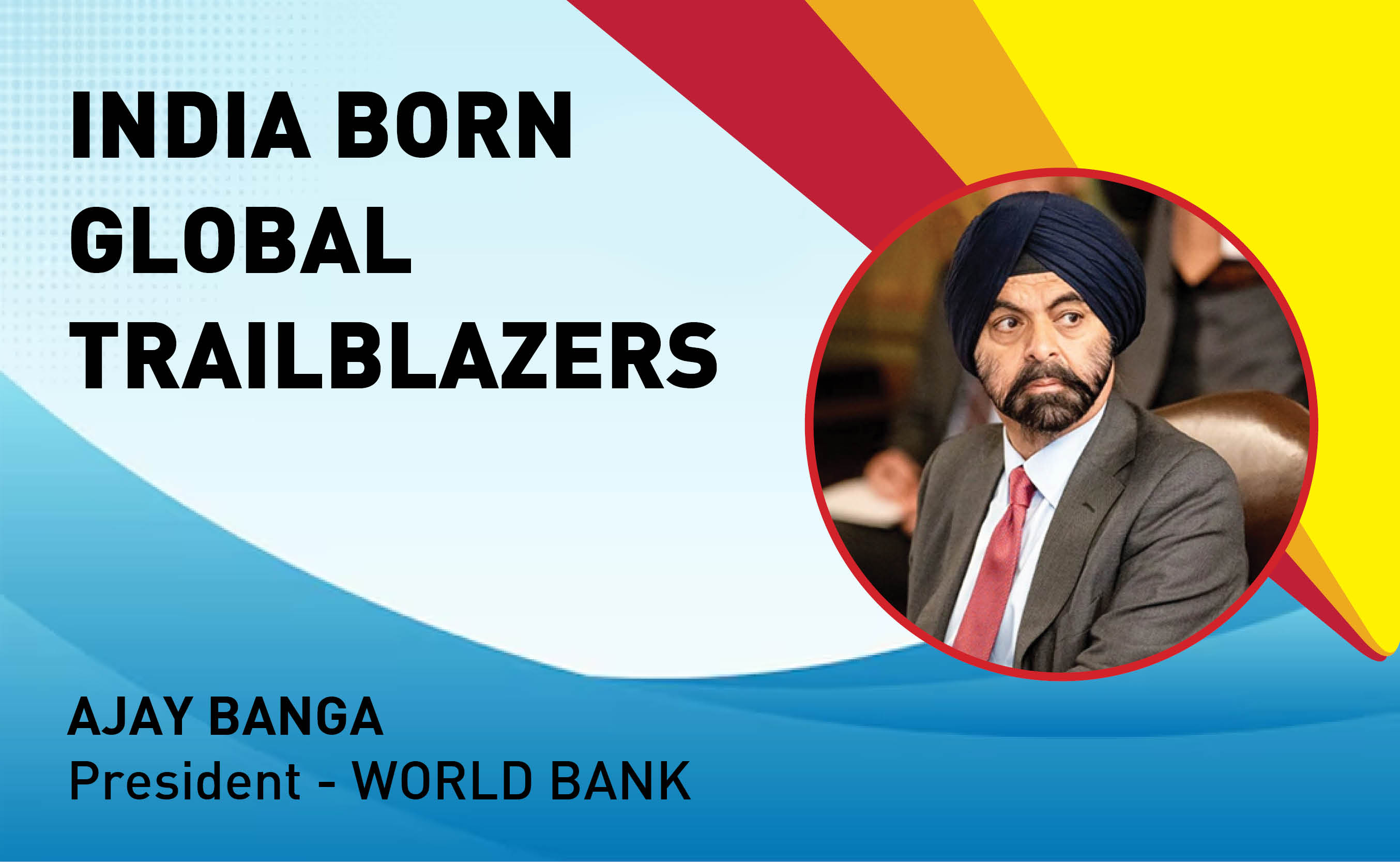
Indian Tech Talent Excelling The Tech World - AJAY BANGA, President - World Bank
Ajay Banga is an Indian-born American business executive who currently...
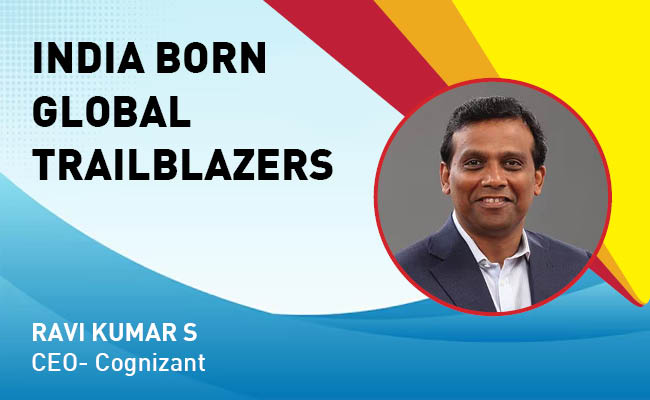
Indian Tech Talent Excelling The Tech World - RAVI KUMAR S, CEO- Cognizant
Ravi Kumar S, appointed as CEO of Cognizant in January 2023, sets the ...
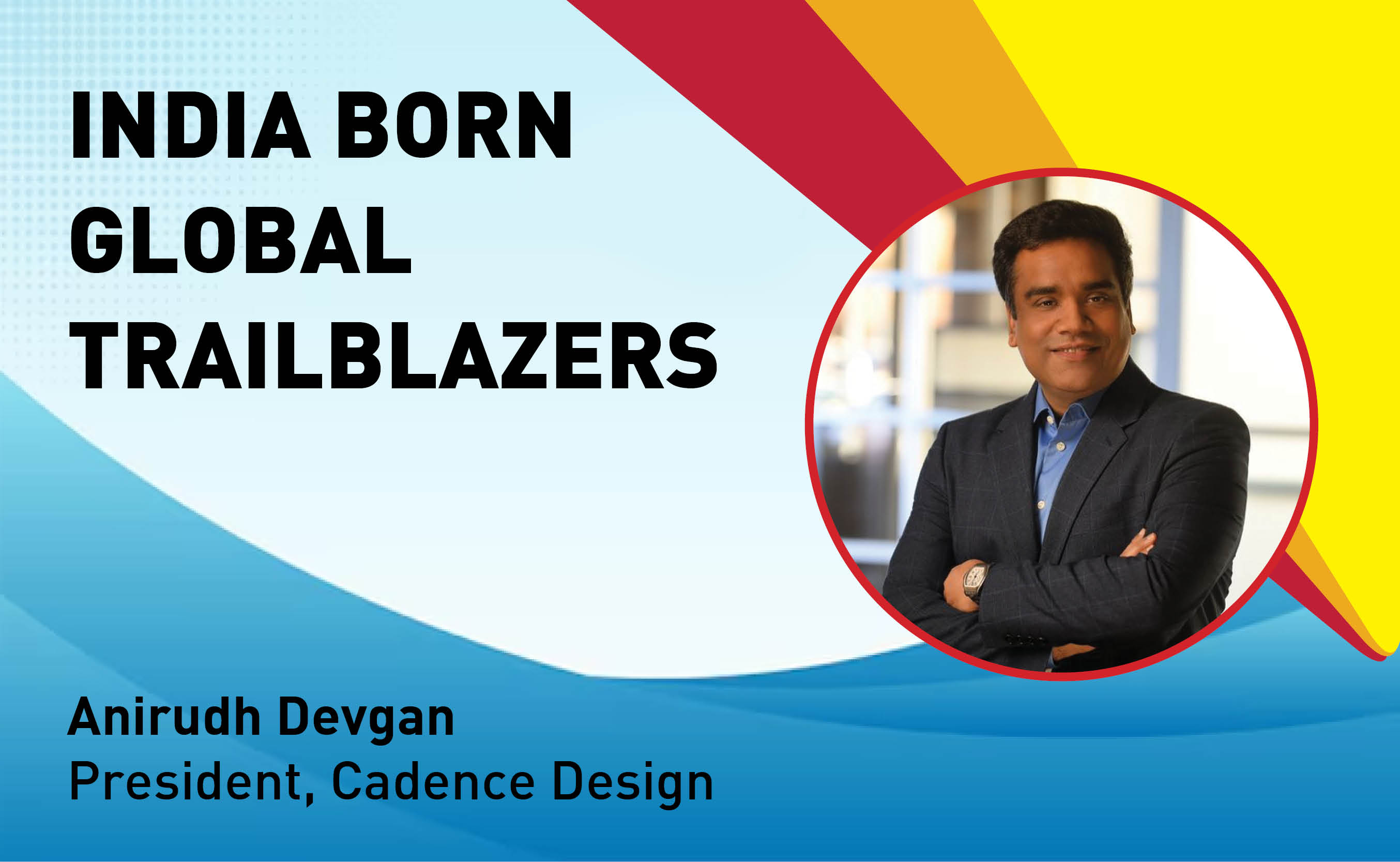
Indian Tech Talent Excelling The Tech World - Anirudh Devgan , President, Cadence Design
Anirudh Devgan, the Global President and CEO of Cadence Design Systems...
 of images belongs to the respective copyright holders
of images belongs to the respective copyright holders