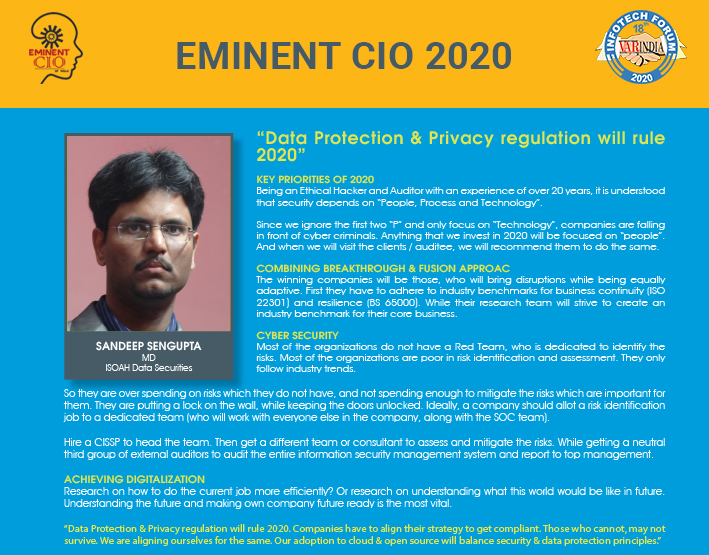
“Data Protection & Privacy regulation will rule 2020”
By MYBRANDBOOK

Sandeep Sengupta
MD
ISOAH Data Securities
Key Priorities of 2020
Being an Ethical Hacker and Auditor with an experience of over 20 years, it is understood that security depends on “People, Process and Technology”.
Since we ignore the first two “P” and only focus on “Technology”, companies are falling in front of cyber criminals. Anything that we invest in 2020 will be focused on “people”. And when we will visit the clients / auditee, we will recommend them to do the same.
Combining Breakthrough & Fusion approac
The winning companies will be those, who will bring disruptions while being equally adaptive. First they have to adhere to industry benchmarks for business continuity (ISO 22301) and resilience (BS 65000). While their research team will strive to create an industry benchmark for their core business.
Cyber Security
Most of the organizations do not have a Red Team, who is dedicated to identify the risks. Most of the organizations are poor in risk identification and assessment. They only follow industry trends.
So they are over spending on risks which they do not have, and not spending enough to mitigate the risks which are important for them. They are putting a lock on the wall, while keeping the doors unlocked. Ideally, a company should allot a risk identification job to a dedicated team (who will work with everyone else in the company, along with the SOC team).
Hire a CISSP to head the team. Then get a different team or consultant to assess and mitigate the risks. While getting a neutral third group of external auditors to audit the entire information security management system and report to top management.
Achieving Digitalization
Research on how to do the current job more efficiently? Or research on understanding what this world would be like in future. Understanding the future and making own company future ready is the most vital.
“Data Protection & Privacy regulation will rule 2020. Companies have to align their strategy to get compliant. Those who cannot, may not survive. We are aligning ourselves for the same. Our adoption to cloud & open source will balance security & data protection principles.”


Legal Battle Over IT Act Intensifies Amid Musk’s India Plans
The outcome of the legal dispute between X Corp and the Indian government c...

Wipro inks 10-year deal with Phoenix Group's ReAssure UK worth
The agreement, executed through Wipro and its 100% subsidiary,...

Centre announces that DPDP Rules nearing Finalisation by April
The government seeks to refine the rules for robust data protection, ensuri...

Home Ministry cracks down on PoS agents in digital arrest scam
Digital arrest scams are a growing cybercrime where victims are coerced or ...


ICONS OF INDIA : VIJAY SHEKHAR SHARMA
Vijay Shekhar Sharma is an Indian technology entrepreneur and multimil...

Icons Of India : Harsh Jain
Harsh Jain, the co-founder of Dream 11, the largest fantasy sports web...

Icons Of India : Girish Mathrubootham
Girish Mathrubootham is the Founder of Freshworks (previously known ...


GeM - Government e Marketplace
GeM is to facilitate the procurement of goods and services by various ...

IOCL - Indian Oil Corporation Ltd.
IOCL is India’s largest oil refining and marketing company ...

EESL - Energy Efficiency Services Limited
EESL is uniquely positioned in India’s energy sector to address ener...


Indian Tech Talent Excelling The Tech World - REVATHI ADVAITHI, CEO- Flex
Revathi Advaithi, the CEO of Flex, is a dynamic leader driving growth ...
Indian Tech Talent Excelling The Tech World - Aneel Bhusri, CEO, Workday
Aneel Bhusri, Co-Founder and Executive Chair at Workday, has been a le...
Indian Tech Talent Excelling The Tech World - Soni Jiandani, Co-Founder- Pensando Systems
Soni Jiandani, Co-Founder of Pensando Systems, is a tech visionary ren...
 of images belongs to the respective copyright holders
of images belongs to the respective copyright holders