Alert issued to the Telegram users, attack from Trojan malware to mount
By MYBRANDBOOK

By embedding code inside a dangerous remote access Trojan, called ToxicEye, hackers are exploiting the Telegram messaging app. ToxicEye can help them take control of computers remotely, as per researchers at Check Point Software Technologies. How powerful is this malware? The ToxicEye remote access Trojan (RAT) can get inside a PC, leak its data, allow a hacker to remotely control the system and also install ransomware, claim the researchers, who also claim to have tracked over 130 ToxiceEye cyber-attacks in the last 3 months.
According to the researchers, the ToxicEye malware has been used to steal sensitive information from systems like passwords, browsing history, cookies and other system information, delete and transfer data, record audio or video, kill the PC processes, steal clipboard contents, deploy keylogger etc.
As per the researchers, first hackers create a Telegram account with which to operate from and also a dedicated Telegram bot. This gives them the opportunity to connect with other users on Telegram via chat, adding people to groups or sending direct requests by entering the Telegram username of the bot and a query. Next, they bundle the bot token with the ToxicEye RAT or any other malware and send it as an email attachment. An example of the sort of infected attachment is a file named “paypal checker by saint.exe”, the researchers have divulged. Users open that email, which leads to their system being connected to the Telegram account of the hacker, which then opens a channel for nefarious activities. After they have opened that email, it doesn’t matter if they have Telegram installed on their computer or not. Since the Trojan has been implanted with the help of an email attachment, even deleting the Telegram app from their system won’t break up the connection of the device with the hacker’s Telegram account.

InterGlobe’s Rahul Bhatia and C.P. Gurnani together announce
In a move that is set to transform the AI landscape, Rahul Bhatia, Group M...
Download masked Aadhaar to improve privacy
Download a masked Aadhaar from UIDAI to improve privacy. Select masking w...

Sterlite Technologies' Rs 145 crore claim against BSNL rejecte
An arbitrator has rejected broadband technology company Sterlite Technolog...

ID-REDACT® ensures full compliance with the DPDP Act for Indi
Data Safeguard India Pvt Ltd, a wholly-owned subsidiary of Data Safeguard ...


Technology Icons Of India 2023: Lt Gen (Dr.) Rajesh Pant (Retd.)
LT Gen(Dr.) Rajesh Panth (Retd.), National cyber security coordination...

Technology Icons Of India 2023: Honorary Prof. N. Balakrishnan
Prof. N. Balakrishnan is an Indian aerospace and computer scientist. H...

Technology Icons Of India 2023: Rajiv Srivastava
Rajiv Srivastava is the Managing Director of Redington Group. With 35 ...

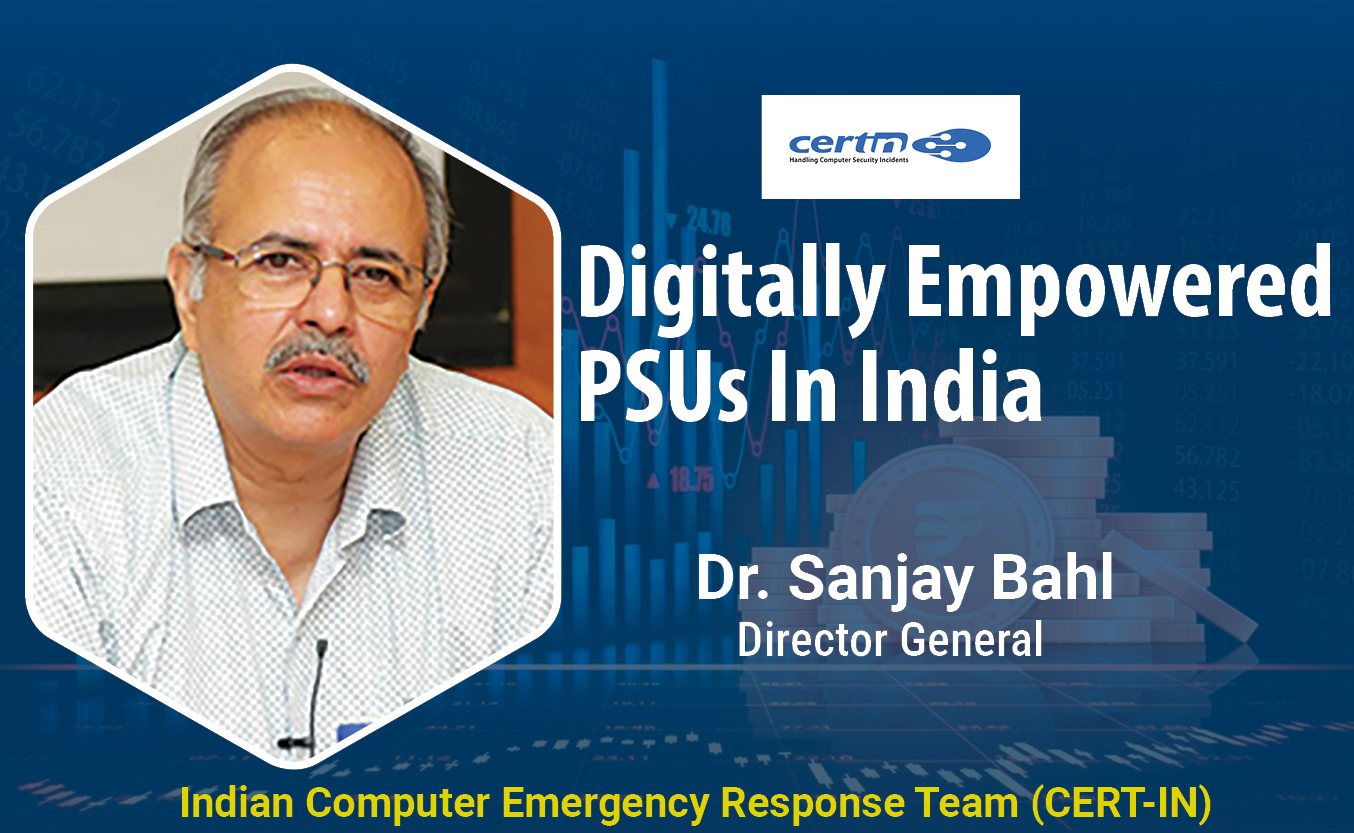
CERT-IN protecting the cyber security space of India
CERT-In serves in the area of cyber security threats like hacking and ...

DRDO is India's largest and most diverse research organisation
DRDO is the R&D wing of Ministry of Defence, Govt of India, with a vis...

STPI encouraging software exports from India
Software Technology Parks of India (STPI) is an S&T organization under...


REDINGTON INDIA LIMITED
Redington (India) Limited operates in the IT product distribution busi...

TEXONIC INSTRUMENTS
Texonic has carved a niche for itself in the Technology Distribution i...

ADITYA INFOTECH LTD.
Aditya Infotech Ltd. (AIL) – the technology arm of Aditya Group, is ...